Urgent: Crypto Exchange Bitrefill Suffers Cyberattack, Lazarus Group Suspected

Crypto e-commerce platform Bitrefill recently announced it was the victim of a sophisticated cyberattack earlier this month, with strong indications pointing to the North Korean-linked Lazarus Group as the likely culprit. The incident, which commenced on March 1, originated from a compromised employee laptop, as detailed in the company's official incident report.
The attackers successfully leveraged legacy credentials associated with Bitrefill’s production systems, enabling them to escalate their access across significant portions of the company's infrastructure. This included segments of its internal database, certain cryptocurrency hot wallets, and its gift card inventory systems. Exploiting this access, the perpetrators managed to drain an undisclosed amount of funds from Bitrefill’s hot wallets. Furthermore, they exploited the gift card inventory to execute suspicious purchases with various vendors. Bitrefill has confirmed that it will absorb all financial losses incurred due to the breach using its operational capital, without specifying the total amount.
The intrusion was first detected through irregular purchasing patterns and unusual supplier activity. In response to the breach, Bitrefill promptly took its systems offline globally to contain the attack. The company has since confirmed that its services, including payments and account access, have been fully restored and are operating at normal levels.
While the primary objective appeared to be financial gain, the attack did lead to a limited exposure of customer data. Approximately 18,500 purchase records were accessed by the attackers, which included customer email addresses, cryptocurrency payment addresses, and metadata such as IP addresses. Of particular concern are about 1,000 of these records which contained encrypted customer names; these are being treated as potentially exposed due to the possibility that the encryption keys were also compromised. Bitrefill has directly notified all affected users.
Bitrefill emphasized its robust data privacy practices, stating that it stores minimal personal data and does not mandate know-your-customer (KYC) verification for the majority of its transactions. Any KYC-related information is managed by external providers and is never stored within Bitrefill's internal systems. The company also stated there is no evidence to suggest that its full database was exfiltrated or that customer data was the primary target of the attack. According to their investigation and logs, the attackers' queries were limited and consistent with probing for high-value assets such like cryptocurrency holdings and gift card inventory, rather than extensive data theft.
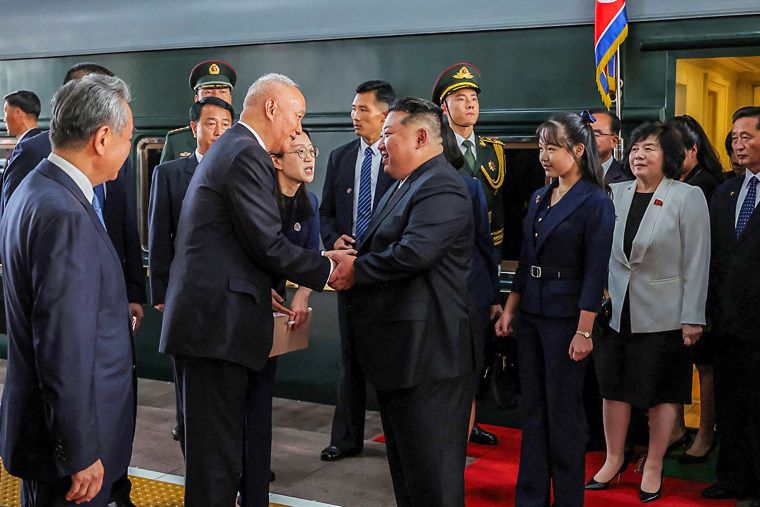
Multiple indicators led Bitrefill to link the attack to the notorious Lazarus Group. These included similarities in malware used, the reuse of specific infrastructure components such as IP addresses and email accounts, and identifiable on-chain transaction patterns. The Lazarus Group, widely associated with North Korea, is known for its specialized subgroup, Bluenoroff, which has been implicated in some of the largest cryptocurrency thefts globally in recent years. Bitrefill received assistance from cybersecurity firms zeroShadow, SEAL911, and RecoverisTeam, along with on-chain analysts and law enforcement, during the incident response and investigation.
This incident underscores the persistent and evolving threat of state-sponsored cyberattacks within the digital asset sector. Analytics from blockchain firm Chainalysis reveal that North Korean-linked groups have been responsible for billions of dollars in crypto thefts in recent years, highlighting the significant scale of illicit activity in this space. Bitrefill is now implementing additional security measures, including expanded monitoring systems and enhanced internal controls, to fortify its defenses against future incursions. The company has expressed confidence in its recovery, noting that customer activity and sales volumes have returned to typical levels post-incident.
You may also like...
Arteta's Reality Check: Arsenal In 'Different World' Than Bayern, PSG

Mikel Arteta praised the PSG vs. Bayern Champions League semifinal as the best game he's seen, attributing its quality t...
Rooney Drops Age Bomb: Salah and Van Dijk Past Their Prime?

Wayne Rooney asserts that Mohamed Salah and Virgil van Dijk are succumbing to age, impacting their performance at Liverp...
Netflix's Gripping Cult-Inspired Thriller Becomes a Global Phenomenon with 46.9 Million Hours Watched
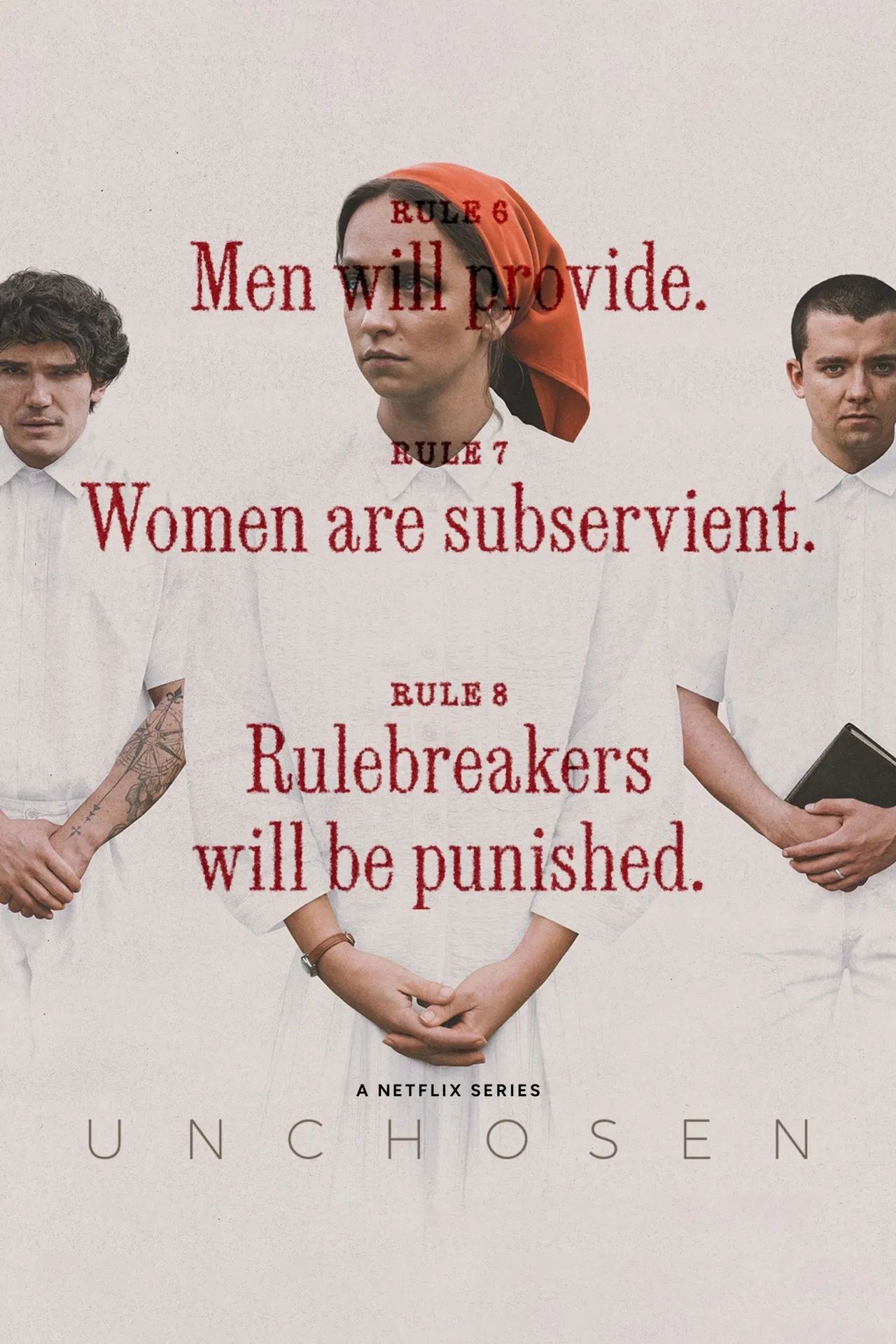
Netflix's new drama series, "Unchosen," delves into the complex world of religious cults, inspired by real survivor stor...
Coachella Magic: Madonna and Geena Davis Share Sweet Reunion, Decades After Iconic Film

Hollywood legends Geena Davis and Madonna reunited on stage at Coachella during Sabrina Carpenter's set, 34 years after ...
Manilow's Health Battle: Legend Delays Vegas Residency Amidst Cancer Recovery Journey

Barry Manilow has postponed his May Las Vegas residency due to ongoing recovery from lung cancer surgery, but anticipate...
Reacher Fans Rejoice: Netflix Drops New Action Thriller for Perfect Weekend Binge!

Director Steven Caple Jr. discusses his pivotal role in shaping Netflix's <em>Man on Fire</em> Season 1, from establishi...
Ted Lasso Star Teases Exclusive Update for Apple TV's Next Sci-Fi Hit!

Juno Temple, celebrated for her role in Ted Lasso, is starring in a new Apple TV+ sci-fi dramedy, The Husbands. The seri...
Replit CEO Amjad Masad Unpacks Cursor Deal, Apple Rivalry & Stance on Selling

Amjad Masad details Replit's explosive growth to a projected billion-dollar annual run rate, emphasizing its unique valu...