The Weakest Link: How Humans endanger Cyber security

Opens Scene
MD: Mr. Adepoju, how are you doing today?
Mr. Adepoju the Data protection officer of Global tech limited, stands to respond "Good morning sir, I am very good sir".
They both take their seats in Mr. Adepoju's office.
MD: you know since you joined our company, we haven't had any data breach of any sorts — all thanks to you. But now that you're leaving ehn, you're leaving a void.... and no clear sense of succession.
ADEPOJU: MD sir, if this is about finding a replacement, I'm not sure I want to be responsible for that. Cyber security is a very delicate field, and I'd rather the company hires someone they feel competent enough.
MD: Ehn, actually it's not even that. I have someone, he's the son of my cousin and I'm sure he can do it excellently.
Latest Tech News
Decode Africa's Digital Transformation
From Startups to Fintech Hubs - We Cover It All.
ADEPOJU: Oh, really?
MD: Yes, of course. Ehn Matthew, you can come in.
Matthew enters the office.
MATTHEW: Good morning, Mr. Adepoju.
ADEPOJU: Good morning, what are your qualifications?
Matthew goes on to explain his certifications and experience. Adepoju leads the M.D out of the office. Adepoju explains that his nephew lacks the experience to take over from him, but the managing director remains persistent. Adepoju finally agrees in a condition that Matthew works alongside him for a couple of months before taking responsibility.
A couple of weeks later, all employees get a mail from the HR concerning salary review — or at least that's what they expected to believe. Most of the employees who had been trained by Mr. Adepoju were able to identify it as a phishing mail.
But poor Matthew, clicks the link with his work laptop, and fills the form using his personalised work mail.
Latest Tech News
Decode Africa's Digital Transformation
From Startups to Fintech Hubs - We Cover It All.
That single click quickly ended the internship of Matthew and Mr. Adepoju was forced to work another year before being able to find a suitable replacement.
HUMAN ERROR IN CYBER SECURITY
In the world of cybersecurity, it only takes one wrong click to undo years of vigilance — and more often than not, that click comes from within. And just like the story of Matthew, many cyber attacks have simply come from mistakes that could have been easily avoided.

In today's world of tech, many companies invest heavily in what they feel protects their data the most — firewalls, antiviruses, encryptions but yet, the most unpredictable vulnerability remains the human behind the keyboard.
The IBM cyber Security Intelligence Index Report provides that 'Human error was a major contributing cause in 95% of all breaches.' Simply put, this means that if human error was somehow dealt with, 19 out of 20 cyber attacks may not have happened at all.
This statistics emphasizes just how much humans are vulnerable to cyber attacks, which most times are caused by variety of unforeseen factors in human behaviour.
In the context of cyber security, human error refers to unintentional actions or inactions by employees and users that can cause, spread or allow a security breach to take place.
Latest Tech News
Decode Africa's Digital Transformation
From Startups to Fintech Hubs - We Cover It All.
This encompasses a vast range of actions from clicking a phishing link, downloading a malware-infected attachment to failing to use a strong password — which is part of the reason why it can be so difficult to address.
And the creation of more advanced and maybe complicated work environments have only made it more difficult for the human side. Employees now have to juggle countless tools, platforms and passwords every day. Each platform demands it's own login credentials, and in the absence of user-friendly or secure alternatives, people inevitably resort to taking shortcuts — writing passwords down, reusing weak ones or sharing access credentials informally.
These small, seemingly harmless habits have proven to be enough to cause the most catastrophic breaches ever.
As if this wasn't a lot to deal with already, employees now face constant exposure to increasingly sophisticated social engineering tactics. Cyber criminals no longer rely on complex code as they now exploit human psychology instead.
Phishing emails, urgent text messages and deceptive websites have been designed to manipulate trust, create curiousity or fear prompting users to hand over sensitive information without realising it.
This evolving manipulation of human behavior has made social engineering one of the most potent tools in modern cybercrime, capable of breaching even the most advanced digital defenses.
COMMON FORMS OF HUMAN-CAUSED BREACHES
While human errors in cyber security can take many forms, they can be generalised under two major categories — skill based errors and decision based errors and understanding this distinction helps organisations design more effective responses, since not all mistakes stem from ignorance as lapses in attention and routine behaviour are major factors as well.
Latest Tech News
Decode Africa's Digital Transformation
From Startups to Fintech Hubs - We Cover It All.
Skill-Based Errors: This error occurs when the employee knows the correct procedure but fails to execute it properly due to distractions, fatigue or momentary carelessness. This can happen in various ways, some of them are;
Misdelivery of Sensitive Data: Misdelivery - sending something to a wrong recipient - is a common threat to corporate data security. According to Verizon’s 2018 breach report, misdelivery was the fifth most common cause of all cyber security breaches.
This problem has mainly been attributed to relying on features such as auto-suggest in their email clients. Till today, one of the most serious case of misdelivery remains the NHS' releasing of the email addresses and by implication names of over 800 patients who had visited HIV clinics.
This unfortunate incident came when an employee sending out an email notification to HIV patients accidentally entered their email addresses to the “to” field, rather than the “bcc” field, exposing their details to each other.
Some other skill based errors can come from the failure of companies to install security updates. This problem which could emanate from negligence or ignorance has caused tragic problems like the 2017 WannaCry Ransome attack, which exploited systems that had not installed a readily available Microsoft patch.
Decision Based Errors: This kind of errors occur when users make the wrong choice due to misinformation, lack of awareness, or poor judgement. Some types of decision making errors are;
Phishing and Social Engineering Attacks: Here, employees fall for deceptive emails or messages designed to steal sensitive information or install malwares. This happens when users fail to identify the obvious in fraudulent communication or mails. In essence, this is an decision-based error rooted in insufficient awareness.

Latest Tech News
Decode Africa's Digital Transformation
From Startups to Fintech Hubs - We Cover It All.
Some other forms are weak and reused passwords. A National Centre for Cyber Security’s 2019 report cast a dire image: 123456 remains the most popular password in the world, and 45% of people reuse the password of their main email account on other services. Such moves from employees — choosing convenience over security, has been quickly exploited by hackers.
Human error isn't just a technical glitch — it's an expensive vulnerability. According to IBM’s Cost of a Data Breach Report (2024), the global average cost of a data breach has risen to $4.45 million, marking a 15% increase over the last three years. A significant portion of these breaches are traced back to employee mistakes such as misdirected emails, weak passwords, or falling for phishing scams.
Beyond the financial toll, human-caused breaches cause significant damage to the reputation of a company. Breaches like this can deter the confidence customers and investors have in them and if not managed properly, this can cause companies to collapse.
PREVENTIVE MEASURES AND SOLUTIONS
Combating cyber security issues isn't as easy as it would seem, as even the best preventive measures can fail. But here's how best to prevent these errors.
Reduction of Opportunities: Companies can reduce the opportunity hackers get to infiltrate their systems. This can be done through various means, like privilege access which requires giving employees access to only what they need to do their jobs efficiently, the use of two factor authentication across your business to add an extra layer of protection to your accounts and a simple change in culture.
This can be done by encouraging discussions about cyber security, creating an environment where people are free to ask questions, and the use of tips and reminders to help employees protect themselves and the companies.
Training employees has also been proven to be useful and effective as well, and this was emphasized in the fictional story shared earlier.
Latest Tech News
Decode Africa's Digital Transformation
From Startups to Fintech Hubs - We Cover It All.
Ultimately, it is pertinent to understand that humans don't have to be the weakest link. But maybe it's a good thing, because it means that if conscious efforts are made to correct them to the latter, reducing human error can create huge gains in security.
Recommended Articles
You may also like...
NBA Playoffs Electrify: Thunder Dominate Spurs in Game 3 Thriller!

The Oklahoma City Thunder defeated the San Antonio Spurs 123-108 in Game 3 of the Western Conference finals, taking a 2-...
Premier League Shocker: Bruno Fernandes Crowned Player of the Season!

Bruno Fernandes has been named the Premier League Player of the Season, an award he secures for the first time while equ...
Netflix Unleashes Global Sci-Fi Phenomenon, Hailed as Next 'Stranger Things'
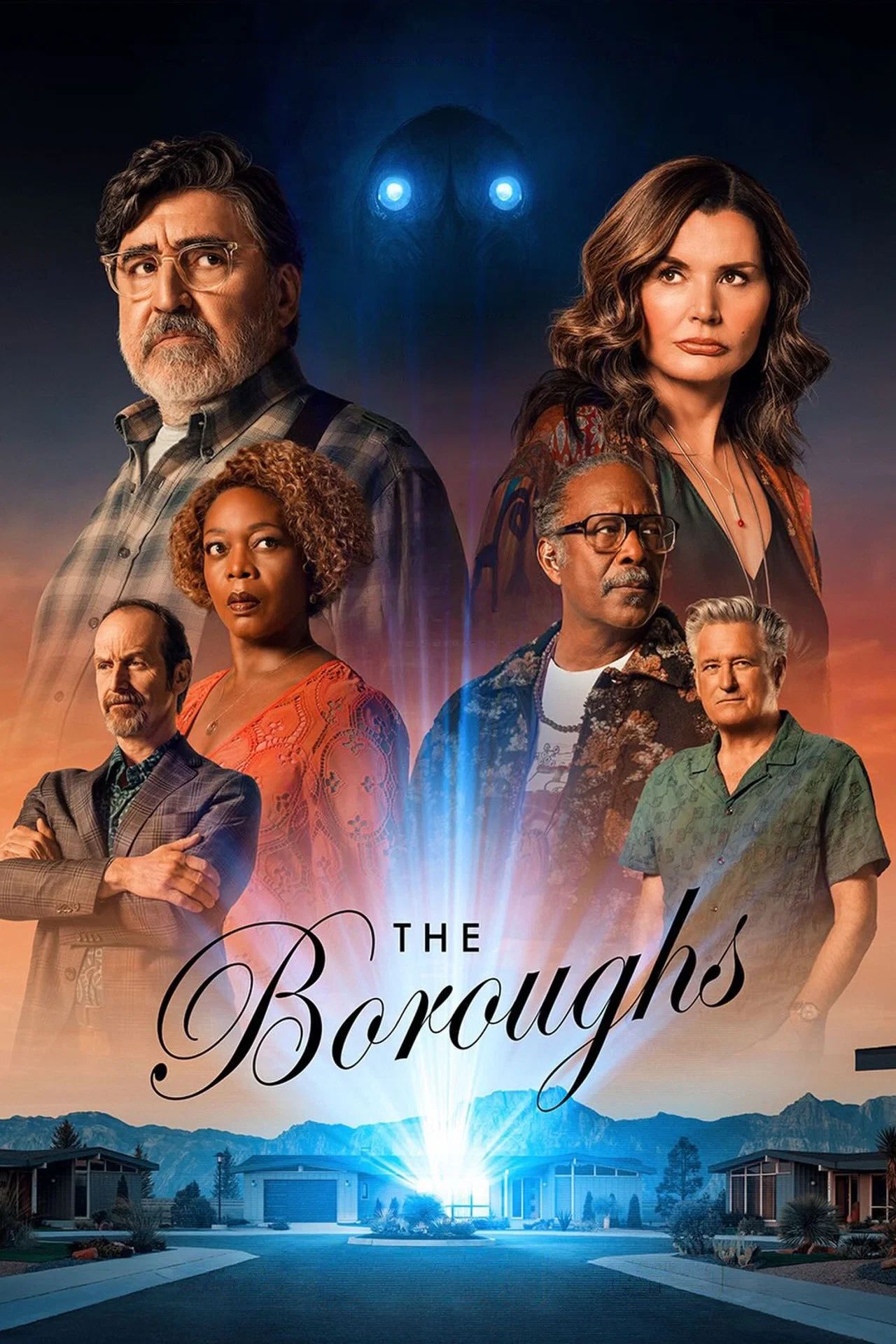
Netflix's new sci-fi series "The Boroughs," executive-produced by the Duffer Brothers, has soared to the top of viewersh...
Cannes Market Frenzy: Netflix and Mubi Battle for Hot Titles

The Cannes Film Market buzzes with major acquisitions as Netflix secures two high-profile films, "La Bola Negra" and "Ge...
ASIAN KUNG-FU GENERATION Rocks 30th Anniversary With Brand New EPs!

ASIAN KUNG-FU GENERATION recently released their 'Fujieda EP' and single 'Skins,' recorded at the unique MUSIC inn Fujie...
Post Malone Unleashes Epic Australian & New Zealand Stadium Tour!

Post Malone is bringing his "Big Ass World Tour" to Australia and New Zealand this October for his largest headline show...
US Imposes Sanctions on Tanzanian Police Over Activist Torture Claims

The United States has sanctioned senior Tanzanian police official Faustine Jackson Mafwele for gross human rights violat...
Ebola Threat Surges in Eastern DR Congo as UN Ramps Up Response

The UN is accelerating its response to a rapidly escalating Ebola outbreak in eastern DRC, where conflict and deep mistr...

